Symmetry | Free Full-Text | Encryption Techniques for Smart Systems Data Security Offloaded to the Cloud

Use of the Advanced Encryption Standard Algorithm for Encryption Short Message Service on Real Count Applications | Semantic Scholar

Types of Encryption: 5 Encryption Algorithms & How to Choose the Right One - Hashed Out by The SSL Store™

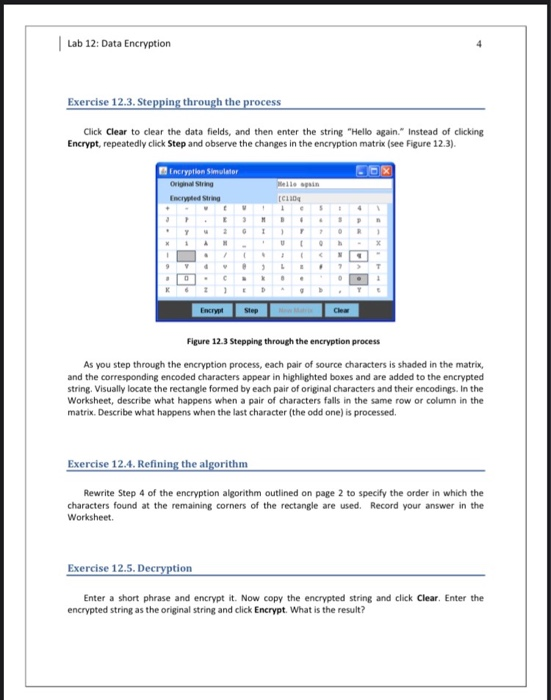
![What Is Data Encryption: Algorithms, Methods and Techniques [2022 Edition]| Simplilearn What Is Data Encryption: Algorithms, Methods and Techniques [2022 Edition]| Simplilearn](https://www.simplilearn.com/ice9/free_resources_article_thumb/What_are_the_Most_Effective_Data_Encryption_Techniques.jpg)